Try Google Drive for yourself → https://goo.gle/3M72zNs
Read Full
This video demonstrates how SentinelOne’s Singularity™ Identity protects against LSASS Credential Dumping attacks. LSASS Credential Dumping is a common tactic used by threat actors to extract sensitive credentials from Windows
Read Full
This video demonstrates how SentinelOne’s Singularity™ Identity protects against LSASS Credential Dumping attacks. LSASS Credential Dumping is a common tactic used by threat actors to extract sensitive credentials from Windows
Read Full
This video demonstrates how SentinelOne’s Singularity™ Identity protects against LSASS Credential Dumping attacks. LSASS Credential Dumping is a common tactic used by threat actors to extract sensitive credentials from Windows
Read Full
Synology Photos was designed to allow you to conveniently keep and securely back up photo and video memories from your mobile devices to your Synology NAS with just a few
Read Full
What is Google Workspace → https://goo.gle/3SCXS07
Read Full
Vulnerabilities in System Management Mode (SMM) and more general UEFI applications/drivers (DXE) are receiving increased attention from security researchers. Over the last 12 months, the Binarly efiXplorer team disclosed 107
Read Full
The US is still lagging behind China in terms of vulnerability discovery and disclosure. While the gap between the US National Vulnerability Database (NVD) and the Chinese NVD (CNNVD) has
Read Full
You can even add your own for later use!
Read Full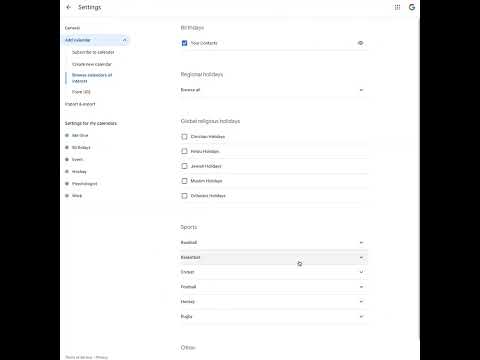
Try Google Calendar for yourself → https://goo.gle/3EhDGNk
Read Full